Arthur Besse
cultural reviewer and dabbler in stylistic premonitions
- 25 Posts
- 199 Comments
To answer your question: yes, YTA 🤦
Also, I’m deleting this post per asklemmy rule 3.

 11·20 days ago
11·20 days agoThe tone which comes across in the video (linked from the other post I linked to in this post’s description) is unfortunately much less amicable than this article conveys.

 61·20 days ago
61·20 days agothe guy speaking off camera in the linked 3min 30s of the video is Ted Ts’o, according to this report about the session.
That pin can be found for $30 or $35 on on ebay here and here, where it is described as being from the 80s and as an “employee pin”.
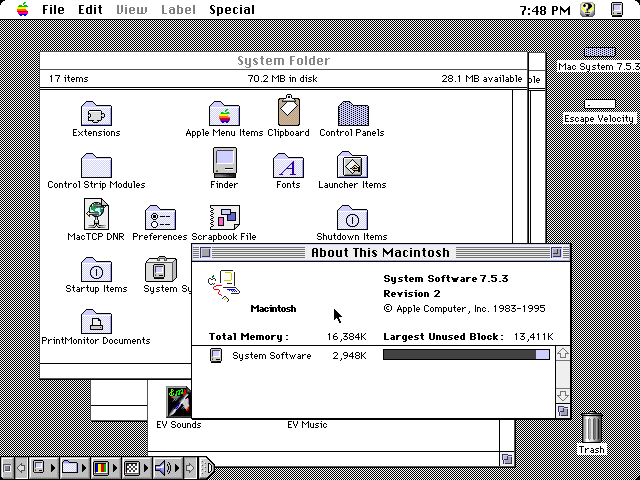
I was thinking that this might have been something aimed specifically at technology buyers in US schools in the 80s or 90s, to whom Apple offered substantial institutional discounts in a (relatively successful) effort to dominate that sector. However searching the phrase “does more costs less” i found this TV spot advertising the Quadra 605 which at $1000 was the cheapest computer Apple sold when it was introduced in October 1993 (and allegedly cheaper than something else they refer to as “PC Leading Brand” 😂). That system was sold under the LC and Performa brands up to 1996, but it was only sold as a Quadra until October 1994, so, to answer OP’s question: that slogan was in use at least sometime in that year.

 5·2 months ago
5·2 months agoIt looks like Framework only offers entry-level Radeon GPUs.
If you want to do GPU compute in a laptop and money is no object, something from Lenovo’s Legion series of gaming laptops is probably a good choice. You can get one with an RTX 4090 in it, and the series (or many models of it, at least) appears to have reasonably good Linux support. (Disclaimer: I’ve never used one.)

 2·2 months ago
2·2 months agoi think /c/politics@lemmy.ml was removed due to redundancy with /c/worldnews@lemmy.ml more than /c/usa@lemmy.ml.
that’s not to say it couldn’t be a place for non-news-related political discussions, but in practice it mostly got posts which would fit in worldnews.
it could be restored if one or more users with a good history wants to take responsibility for moderating it.
If you’re interested in using something other than Microsoft Windows, getgnulinux.org is a good place to read about your options and how to switch.

 6·2 months ago
6·2 months agoadding all compiled file types including .pyc to .gitignore would fix it
But in this case they didn’t accidentally put the token in git; the place where they forgot to put
*.pycwas.dockerignore.

 9·2 months ago
9·2 months agoAt my workplace, we use the string @nocommit to designate code that shouldn’t be checked in
That approach seems useful but it wouldn’t have prevented the PyPI incident OP links to: the access token was temporarily entered in a
.pypython source file, but it was not committed to git. The leak was via.pyccompiled python files which made it into a published docker build.
python -c 'print((61966753*385408813*916167677<<2).to_bytes(11).decode())'how?
$ python >>> b"Hello World".hex() '48656c6c6f20576f726c64' >>> 0x48656c6c6f20576f726c64 87521618088882533792115812 $ factor 87521618088882533792115812 87521618088882533792115812: 2 2 61966753 385408813 916167677

 41·3 months ago
41·3 months agoi guess maybe if you’re using a device with a tiny screen and a lemmy client that doesn’t let you zoom in on images

 1313·3 months ago
1313·3 months agoshoutout to the person who reported this post with “Reason: Bot meme, you can’t even read it. whoever replies is a bot too” 😂

 16·4 months ago
16·4 months agoYou may not like it, but this is what peak performance looks like.

 2·4 months ago
2·4 months agoE: old thinkpad gang input: take the time to reapply thermal grease to the cpu at some point. It makes a huge difference.
What’s a “gang input”?
😂 it’s an input to this discussion from a member of the group of people (“gang”) who have experience with old thinkpads. and yes, if your old thinkpad (or other laptop) is overheating and crashing, reapplying the thermal paste is a good next step after cleaning the fans.

 5·4 months ago
5·4 months agoxzbot from Anthony Weems enables to patch the corrupted liblzma to change the private key used to compare it to the signed ssh certificate, so adding this to your instructions might enable me to demonstrate sshing into the VM :)
Fun :)
Btw, instead of installing individual vulnerable debs as those kali instructions I linked to earlier suggest, you could also point debootstrap at the snapshot service so that you get a complete system with everything as it would’ve been in late March and then run that in a VM… or in a container. You can find various instructions for creating containers and VMs using debootstrap (eg, this one which tells you how to run a container with
systemd-nspawn; but you could also do it with podman or docker or lxc). When the instructions tell you to rundebootstrap, you just want to specify a snapshot URL likehttps://snapshot.debian.org/archive/debian/20240325T212344Z/in place of the usual Debian repository url (typicallyhttps://deb.debian.org/debian/).

 27·4 months ago
27·4 months agoA daily ISO of Debian
testingor Ubuntu 24.04 (noble) beta from prior to the first week of April would be easiest, but those aren’t archived anywhere that I know of. It didn’t make it in to any stable releases of any Debian-based distros.But even when you have a vulnerable system running sshd in a vulnerable configuration, you can’t fully demo the backdoor because it requires the attacker to authenticate with their private key (which has not been revealed).
But, if you just want to run it and observe the sshd slowness that caused the backdoor to be discovered, here are instructions for installing the vulnerable liblzma deb from snapshot.debian.org.

 1·5 months ago
1·5 months agoYou can use Wireshark to see the packets and their IP addresses.
https://www.wireshark.org/download.html
https://www.wireshark.org/docs/
A word of warning though: finding out about all the network traffic that modern software sends can be deleterious to mental health 😬

 2·5 months ago
2·5 months agoI do have wireguard on my server as well, I guess it’s similar to what tailscale does?
Tailscale uses wireguard but adds a coordination server to manage peers and facilitate NAT traversal (directly when possible, and via a intermediary server when it isn’t).
If your NAT gateway isn’t rewriting source port numbers it is sometimes possible to make wireguard punch through NAT on its own if both peers configure endpoints for eachother and turn on keepalives.
Do you know if Yggdrasil does something similar and if we exchange data directly when playing over Yggdrasil virtual IPv6 network?
From this FAQ it sounds like yggdrasil does not attempt to do any kind of NAT traversal so two hosts can only be peers if at least one of them has an open port. I don’t know much about yggdrasil but from this FAQ answer it sounds like it runs over TCP (so using TCP applications means two layers of TCP) which is not going to be conducive to a good gaming experience.
Samy Kamkar’s amazing pwnat tool might be of interest to you.





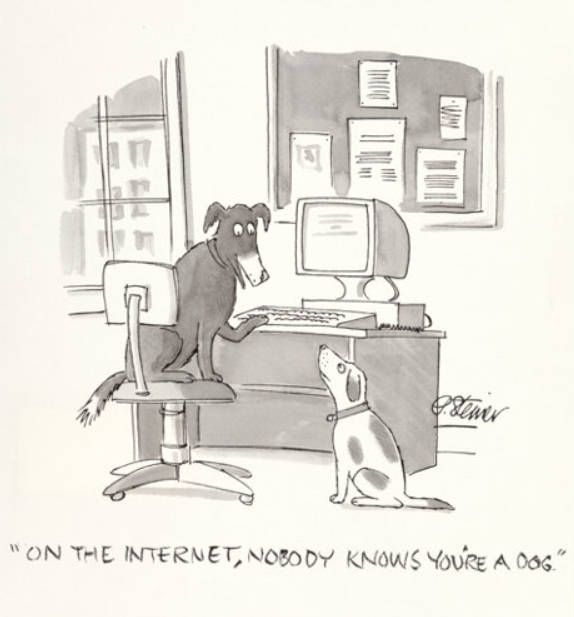




Neither did this guy.
The difference is that LLM output is (in the formal sense) bullshit.